In recent years, drones—officially known as unmanned aerial vehicles (UAVs)—have transitioned from niche gadgets to pivotal tools in security surveillance. Their ability to provide real-time aerial views has revolutionized monitoring practices across various sectors. However, as their integration into security frameworks deepens, so do the associated cybersecurity challenges. This article delves into the transformative impact of drones on security surveillance and offers strategies to mitigate emerging threats.
The Evolution of Drone-Assisted Surveillance
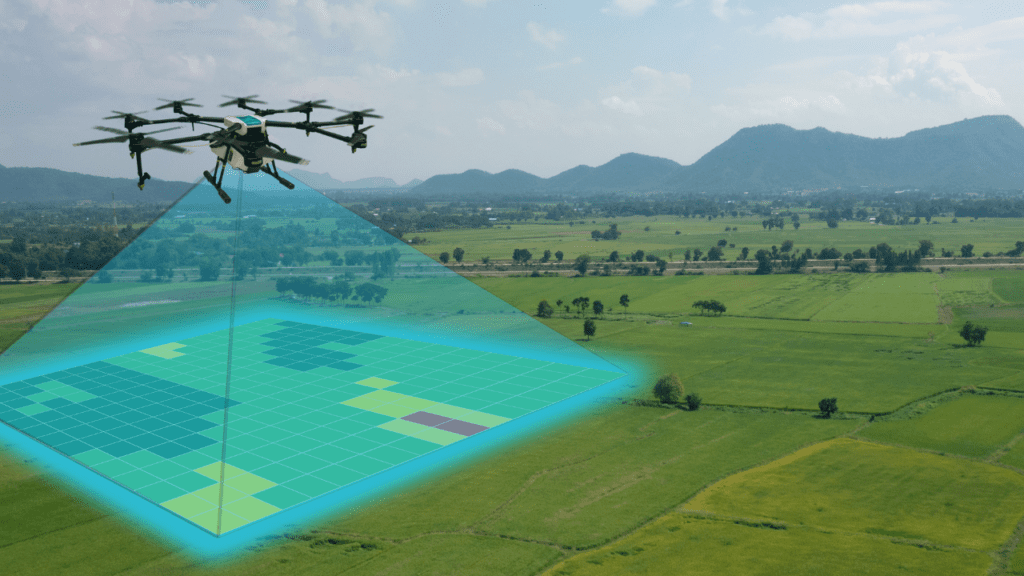
Drones have become indispensable in enhancing situational awareness for security professionals. Their applications span from monitoring large-scale public events to securing critical infrastructure. For instance, law enforcement agencies deploy drones to oversee crowds during events, ensuring public safety and rapid response to incidents. In the private sector, companies utilize drones to patrol expansive properties, detect unauthorized access, and monitor for potential threats.
The advantages of drone surveillance are manifold:
- Cost-Effectiveness: Drones reduce the need for manned patrols and expensive surveillance infrastructure.
- Flexibility: They can access hard-to-reach areas and provide real-time data.
- Enhanced Data Collection: Equipped with high-resolution cameras and sensors, drones capture detailed imagery and environmental data.
Cybersecurity Concerns in Drone Surveillance
Despite their benefits, drones introduce significant cybersecurity vulnerabilities:
- Unauthorized Access: Weak authentication mechanisms can allow adversaries to hijack drones, gaining control over their operations. OWASP
- Data Interception: Unsecured communication channels may enable interception of sensitive data, such as live video feeds or control commands. OWASP
- Malware Insertion: Compromised drones can serve as vectors for malware, potentially infiltrating connected networks.
- Physical Threats: Drones can be weaponized or used for illicit surveillance, posing direct security risks. IoT World Today
Recent Incidents Highlighting Drone-Related Threats
Several incidents underscore the pressing need to address drone-related cybersecurity threats:
- Military Base Intrusions: In December 2024, drones were spotted near at least 17 U.S. military bases adjacent to Chinese-owned land, raising espionage concerns. New York Post
- Unauthorized Airspace Breaches: New Jersey reported a surge in drone sightings over critical areas, prompting Governor Phil Murphy to warn about the nation’s vulnerability to drone incursions. New York Post
- Corporate Espionage: There have been instances where drones equipped with cyber-spying tools were used to breach corporate networks, highlighting their potential in facilitating cyberattacks. Dark Reading
Mitigation Strategies: Strengthening Drone Security
To counteract these threats, organizations should consider the following measures:
- Implement Strong Authentication: Utilize multi-factor authentication and robust encryption to prevent unauthorized access to drone systems. OWASP
- Secure Communication Channels: Ensure all data transmissions between drones and control systems are encrypted to protect against interception. OWASP
- Regular Software Updates: Keep drone firmware and associated software up to date to mitigate vulnerabilities.
- Conduct Security Audits: Perform regular assessments of drone systems to identify and address potential security weaknesses.
- Establish No-Fly Zones: Define and enforce no-fly zones to prevent unauthorized drone operations over sensitive areas.
- Deploy Anti-Drone Technologies: Invest in technologies capable of detecting and neutralizing unauthorized drones.
- Educate Personnel: Train staff on the potential risks associated with drones and the importance of cybersecurity best practices.
- Develop Incident Response Plans: Establish protocols to respond effectively to drone-related security incidents.
- Collaborate with Authorities: Work closely with regulatory bodies and law enforcement to stay informed about emerging threats and compliance requirements.
- Monitor Airspace Activity: Utilize airspace monitoring tools to detect and assess drone activities in the vicinity of critical infrastructure.
Conclusion
Drones have undeniably transformed security surveillance, offering unprecedented capabilities in monitoring and data collection. However, their integration into security operations introduces complex cybersecurity challenges that must be addressed proactively. By implementing robust security measures and fostering a culture of vigilance, organizations can harness the benefits of drone technology while safeguarding against potential threats.