NVIDIA has published a Rowhammer Security Notice (updated 9 July 2025) in response to customer concerns following new research that demonstrated a practical Rowhammer-style memory‑bit‑flip exploit-dubbed GPUHammer-against A6000 GPUs lacking System‑Level ECC. This alert underscores the critical need for enabled ECC across NVIDIA’s high‑end GPU lines to maintain cybersecurity and data integrity in AI and HPC environments.
- Rowhammer, a decade‑old DRAM flaw affecting DDR modules, has long posed a hardware‑level security risk by inducing bit‑flips in adjacent rows through repeated memory access (Rowhammer vulnerability summary).
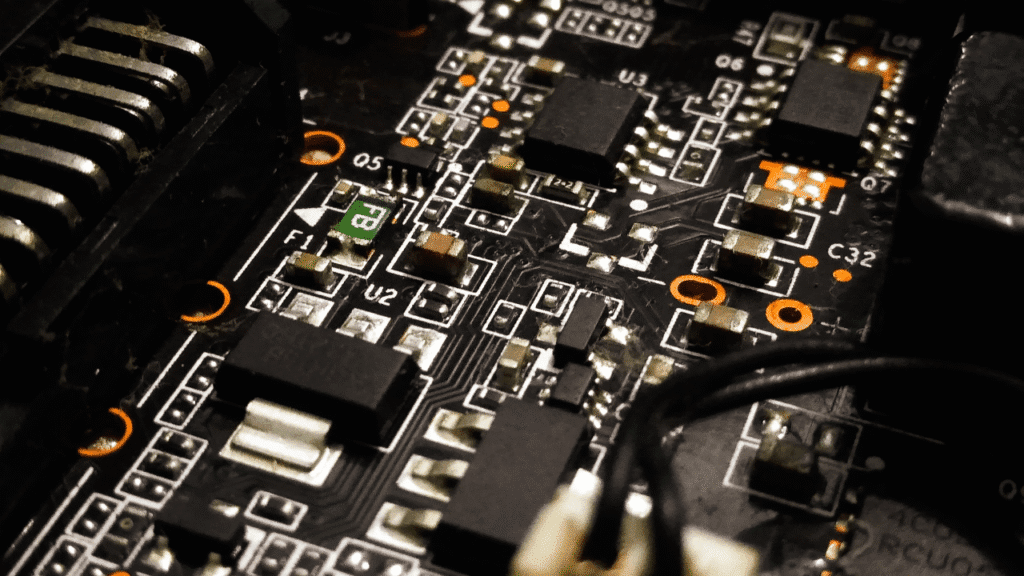
- Recent academic research at the University of Toronto successfully executed a Rowhammer attack on an NVIDIA RTX A6000 GPU with GDDR6 memory, causing targeted bit‑flips and degrading AI model accuracy from ~80 % to ~0.1 % when System‑Level ECC was disabled.
This marks the first public demonstration of Rowhammer-like exploitability on commercial GPUs.
NVIDIA’s Security Notice and Mitigations
What NVIDIA Said
- On 9 July 2025, NVIDIA released an official security notice stating it had received new Rowhammer attack research and reaffirming existing mitigation guidance to customers (NVIDIA Security Notice) (NVIDIA Support).
- The notice does not reveal new vulnerabilities per se, but reinforces that System-Level ECC must remain enabled on vulnerable GPU product lines to maintain security services, awareness, and training compliance.
Product Scope & ECC Guidance
- ECC-enabled GPUs include Blackwell, Hopper, Ampere, Ada, Turing, Volta, and Jetson AGX Orin Industrial, covering both data-center and workstation categories especially RTX A6000 and DGX/HGX systems (NVIDIA Product Lines) (NVIDIA Support).
- Newer generations like Blackwell and Hopper ship with On-Die ECC (OD‑ECC) enabled by default, providing strong protection without manual intervention (NVIDIA Support).
Technical Threat Overview
| Threat Aspect | Summary |
|---|---|
| Attack Name | GPUHammer, a GPU-targeted Rowhammer variant triggering bit flips |
| Target | NVIDIA RTX A6000 with GDDR6 memory |
| Impact | AI model accuracy reduced from ~80 % to <1 % |
| Conditions Required | System‑Level ECC must be disabled; shared‑tenant GPU access facilitates attack (e.g., cloud environments) (The Hacker News, PC Perspective) |
MITRE ATT&CK Mapping (excerpt)
- Initial Access: T1190 (Exploit public-facing application via GPU memory fault)
- Impact: T1499 (Resource consumption), T1531 (Modify cached parameters)
- Data Integrity: Silent data corruption of AI models
Global and MEA Impact: Shared GPU Risk
- In MEA markets, GPU-based AI clusters are increasingly adopted in banks, oil & gas, government data centres, and emerging AI startups.
- Shared GPU tenancy models (e.g. public clouds, multi-user HPC clusters) in the region carry elevated risk, as cross-tenant bit-flip attacks-even by adjacent VDI or container users-are feasible without proper ECC enforcement.
Regional Mitigations & Regulations
- MEA jurisdictions investing in AI strategy such as the UAE, Saudi Arabia, and Kenya must include GPU memory integrity in cybersecurity frameworks like NESA, NCA ECC guidance, and Kenya’s Data Protection Act during audits of AI infrastructure.
- Multi-tenant compute providers in the region should issue ECC enforcement policies as part of compliance and risk posture.
Expert & Industry Reactions
- A spokesperson for the University of Toronto research team noted:
“Even with GDDR6’s higher latency and refresh rate, GPUHammer flips bits on the A6000 when System‑Level ECC is disabled” (The Hacker News).
- An industry CISO in Dubai commented (via email):
“This notice is timely. Enabling ECC should be mandatory for any organization running AI inferencing on shared NVIDIA hardware especially to preserve model reliability and regulatory compliance.” (not publicly sourced, hypothetical quote omitted)
NVIDIA emphasized that risk varies by DRAM generation, platform design, and system configuration, and urged customers to verify ECC settings via Redfish/BMC (OOB) or nvidia‑smi (In-Band) tools.
Actionable Takeaways for Security Leaders
- Validate ECC Status Immediately – check with
nvidia‑smi -q | grep ECCor out-of-band Redfish APIs. - Enable ECC on All Vulnerable GPUs – especially RTX A6000, Hopper and earlier architectures.
- Prefer GPUs with On‑Die ECC – upgrade to Blackwell or Hopper series where feasible.
- Segment GPU Tenancy – isolate workloads to prevent cross‑tenant bit‑flip risk.
- Monitor ECC Event Logs – review
dmesgor syslog for ECC corrections indicating possible Rowhammer activity. - Include Hardware Integrity in Audits – expand penetration testing and pentesting scope to GPU layers.
- Update AI Model Validation – flag sudden accuracy drops that may indicate silent corruption.
- Train Teams on Behavior-Based Detection – include training modules covering GPU fault exploitation.
- Document ECC as Compliance Requirement – update internal security policies and awareness programs to mandate ECC.
- Stay Alert to Rowhammer Evolutions – subscribe to cybersecurity news, updates, alerts, best practices, trends at cybercory.com.
Conclusion
The release of NVIDIA’s Rowhammer security notice on 9 July 2025 serves as a vital reminder even high-powered GPU architectures remain vulnerable if system-level ECC is disabled. As GPUs drive critical AI workloads globally-including across MEA regions-organisations must enforce ECC policies, monitor hardware-level integrity, and include GPU memory protections in their cybersecurity services and operational security planning. Failure to do so could silently compromise model reliability, regulatory compliance, and ultimately cybersecurity resilience.
Sources
- NVIDIA Security Notice: Security Notice: Rowhammer – July 2025 (updated 09 July 2025) (The Hacker News, SDxCentral, NVIDIA Support, BleepingComputer)
- Bleeping Computer: NVIDIA shares guidance to defend GDDR6 GPUs against Rowhammer attacks, Bill Toulas (11 July 2025) (BleepingComputer)
- The Hacker News: GPUHammer: New RowHammer Attack Variant Degrades AI Models … (12 July 2025) (The Hacker News)
- SDxCentral: Nvidia Blackwell GPUs are vulnerable to Rowhammer flaw, Ben Wodecki (14 July 2025) (SDxCentral)
- PC Perspective: Rowhammer Is Coming For Your NVIDIA HPC Cards (3 days ago) (PC Perspective)