Singapore is currently facing ongoing cyber-espionage attacks by the UNC3886 Advanced Persistent Threat (APT) group, an operation directly targeting its critical infrastructure, including energy, healthcare, and communications. The threat, disclosed 18 July 2025 by Coordinating Minister K. Shanmugam, signals a stark escalation in national cybersecurity threats.
This unfolding incident demands heightened vigilance and swift action from CISOs, regulators, and security teams globally.
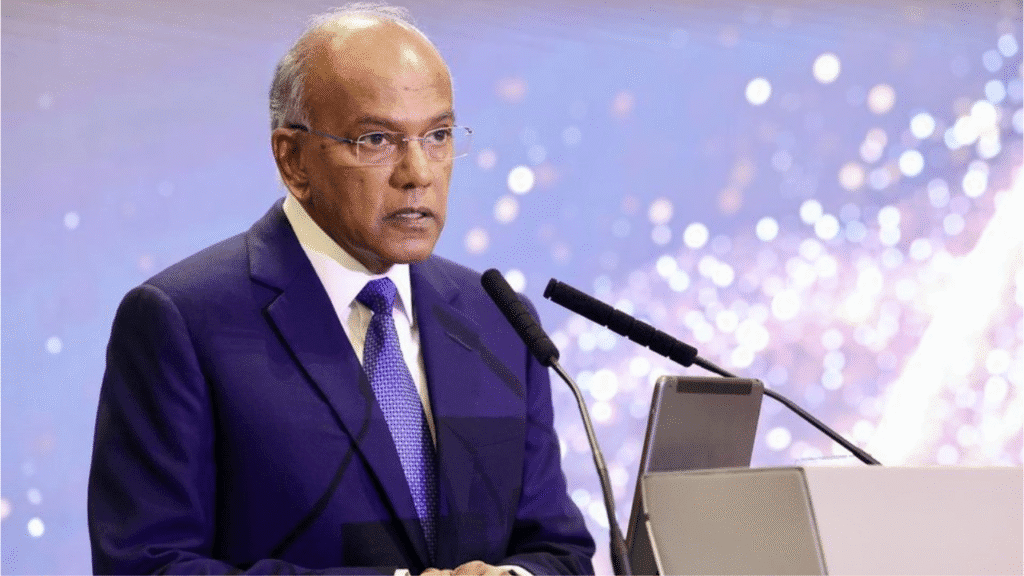
Coordinating Minister for National Security and Home Affairs, K. Shanmugam, disclosed in a speech at the Cyber Security Agency’s 10th-anniversary event that Singapore is being targeted by UNC3886.
He stated:
“UNC3886 poses a serious threat to us, and has the potential to undermine our national security…Even as we speak, UNC3886 is attacking our critical infrastructure right now.”(Reuters)
Details of the attack vector and scale remain classified to protect operational security, though it is confirmed to be ongoing and sophisticated.
Tracking UNC3886
First observed in 2022 by Mandiant, UNC3886 is described as a “China‑nexus espionage group” that has previously targeted defense, telecom, and technology sectors across the U.S. and Asia.
Activity includes deploying custom malware and persistent backdoors on network devices to maintain long-term access.
Scope & Targets of the Attack
APT Activity in Critical Sectors
Minister Shanmugam clarified that the attacks target high‑value sectors-energy, water, finance, transport, and healthcare-undermining public trust and national resilience.
He emphasized the potential cascading impact: a successful breach could disrupt electricity, healthcare, and transportation, crippling essential services and the economy.
Regional Impact and MEA Relevance
Although directed at Singapore, this case serves as a sobering alert for MEA CISOs.
- Terror, transport, and energy systems across MEA are similarly vulnerable.
- Regulatory frameworks like UAE NESA, Saudi NCA ECC, and Kenya Data Protection Act must adapt to counter persistent state-level threats.
Global Context & Comparisons
Similar Incidents Elsewhere
- In April 2025, South Korea reported an attack compromising SIM data of nearly 27 million users.
- Power outages in Ukraine were linked to APT actors highlighting how cyber-espionage can extend to public utilities.
- APT-linked compromises including telecom giants have been attributed to Volt Typhoon and Salt Typhoon.
Scale of APT Threats
Singapore has seen over fourfold increase in suspected APT incidents from 2021 to 2024, per ministerial data a trend mirrored in other geopolitically critical regions.
Expert & Official Statements
- Satnam Narang, Senior Staff Research Engineer at Tenable, commented to Al Arabiya: “Combating such stealthy opponents is becoming increasingly demanding as the scale and complexity of IT infrastructure that organizations and nations must defend continues to grow.”
- The Cyber Security Agency of Singapore (CSA) affirmed it is actively managing the incident and collaborating with critical infrastructure owners to share threat intelligence and conduct defensive actions.
Technical Deep‑Dive: APT Tactics & Tools
MITRE ATT&CK Mapping:
- Valid Accounts: Stealthy backdoor usage
- Masquerading: Custom loader deployment
- Exploit Public-Facing Application: Potential zero-days in routers
- Command and Control: Custom remote shells
- Data Encrypted for Impact: Risk of disruptions or sabotage
Indicators of Compromise (IOCs) are currently classified to maintain ongoing counter-operations.
10 Recommendations for Security Leaders
- Enterprise Network Segmentation: Isolate critical infrastructure from corporate IT environments.
- Deploy Threat Intelligence Sharing: Share IOC and TTP data with peers and regulators.
- Conduct Penetration Testing: Simulate APT behavior via pentesting to uncover vulnerabilities.
- Monitor Emerging Threats: Subscribe to APT radar services and stay informed with cybercory.com for real-time alerts.
- Harden OT/ICS Environments: Secure operational technology (OT) systems using saintynet.com security services, including patch management and authentication controls.
- Enhance Employee Awareness & Training: Regular awareness and phishing simulation exercises are essential to spot early-stage intrusions like spearphishing.
- Zero Trust Implementation: Apply strict identity and access management policies trust nothing by default, even within perimeter defenses.
- Deploy Endpoint Detection & Response (EDR): Implement pentesting and EDR solutions capable of behavioral anomaly detection to mitigate dwell time by APTs.
- Incident Response Plans (IRP): Establish and test coordinated IRPs specific to APT intrusion scenarios.
- Collaborate with Government & Sector CSIRTs: Engage directly with national cyber authorities (e.g., CSA, NCA, NESA) and participate in cross-border security drills.
Conclusion
The revelation that UNC3886, a known China-linked APT group, is actively infiltrating Singapore’s critical infrastructure is a clarion call for nations worldwide to upgrade their cyber readiness. The group’s persistence and stealthy tactics reinforce the urgency of proactive cybersecurity governance, resilience planning, and international cooperation. Singapore’s transparent response is commendable but the battle is far from over. Defenders must assume compromise and act decisively.
Source
Straits Times – UNC3886 attacking Singapore’s critical infrastructure
Reuters – Singapore names UNC3886 as active APT threat
Channel News Asia – Cyber attacks and critical infrastructure
Al Arabiya – UNC3886 threat and APT escalation
The Record – UNC3886 APT campaign analysis
Mandiant – Technical report on UNC3886