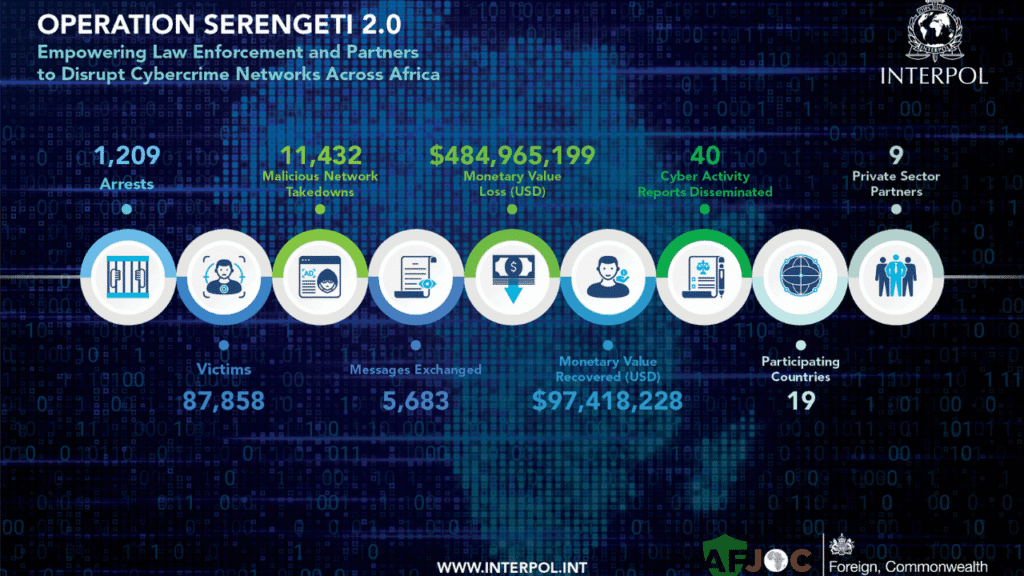
Between June and August 2025, authorities across 18 African nations, coordinated by INTERPOL, arrested 1,209 cybercriminals, dismantled over 11,432 malicious infrastructures, and recovered USD 97.4 million, after nearly 88,000 victims were targeted in sophisticated cyber threats including ransomware, online scams, and business email compromise – a clear demonstration that global collaboration matters now more than ever
Dubbed Operation Serengeti 2.0, the campaign ran from June to August 2025, mobilizing investigators from 18 African countries and the United Kingdom to break down high-impact cybercrime networks identified in INTERPOL’s recent Africa Cyberthreat Assessment Report.
Key Outcomes
- 1,209 individuals arrested for involvement in cybercrime operations.
- USD 97.4 million recovered, alongside dismantling 11,432 malicious infrastructures.
- Nearly 88,000 victims affected across multiple schemes.
Regional Highlights
- Angola: Dismantled 25 cryptocurrency mining centers, illegal operations run by 60 Chinese nationals validating blockchain transactions with 45 illicit power stations and USD 37 million worth of equipment seized. These assets will now support power access in underserved areas.
- Zambia: Uncovered a USD 300 million online investment fraud targeting 65,000 victims. 15 suspects arrested, and investigators seized domains, phone numbers, and bank accounts. A human trafficking ring was also disrupted, with 372 forged passports confiscated.
- Côte d’Ivoire: Busted a transnational inheritance scam linked to Germany, resulting in USD 1.6 million in losses, arrest of the main suspect, and seizure of electronics, jewelry, vehicles, and documents.
Private Sector & International Support
Operation Serengeti 2.0 was enabled by private-sector partners-including Fortinet, Group-IB, Kaspersky, Trend Micro, TRM Labs, Cybercrime Atlas, Shadowserver, Team Cymru, and Uppsala Security-which provided intelligence, training, and technical expertise to participating countries.
Quote from INTERPOL
Valdecy Urquiza, Secretary-General of INTERPOL, stated:
“Each INTERPOL-coordinated operation builds on the last, deepening cooperation, increasing information sharing and developing investigative skills across member countries. With more contributions and shared expertise, the results keep growing in scale and impact. This global network is stronger than ever, delivering real outcomes and safeguarding victims.” (Interpol, Security Affairs)
Actionable Takeaways for Defenders & Executives
- Strengthen cross-border and public–private collaboration, this operation highlights its effectiveness.
- Monitor and identify illicit crypto mining operations, often tied to illegal infrastructure abuse.
- Guard against high-yield investment and inheritance scams, they continue to yield heavy returns for criminals.
- Inspect digital footprints of fraud, including domains, mobile numbers, and suspicious C2 servers.
- Enhance investigative capabilities with OSINT, ransomware, and crypto-forensics training.
- Promote preventive frameworks like InterCOP, to detect and mitigate cyber threats early.
- Support adaptive use of confiscated resources, e.g., redirected power station assets in Angola.
- Track human trafficking and identity fraud interlinkages within cybercrime schemes.
- Keep supply chains tighter with cybersecurity services and pentesting from trusted firms (e.g., saintynet.com).
- Maintain awareness of emerging trends, regularly reviewing cybercory.com for alerts, best practices, and trends.
Conclusion
Operation Serengeti 2.0 underscores the tangible power of international cooperation. With 1,209 arrests, USD 97.4 million recovered, and thousands of victims spared further harm, the campaign demonstrates real progress. For MEA stakeholders-particularly CISOs, SOC leads, regulators, and policymakers-the message is clear: invest in cross-border coordination, proactive threat intelligence, and capacity building now. As cybercriminals adapt, defenders must stay agile, informed, and coordinated across regions to protect digital and physical societies.
Sources
- INTERPOL press release, 22 August 2025 (Interpol)
- AP News, “Large Interpol cybercrime crackdown…”, 22 August 2025 (AP News)
- Help Net Security, “Interpol operation seizes $97 million…”, 22 August 2025 (Help Net Security)
- Security Affairs, “Operation Serengeti 2.0: INTERPOL nabs 1,209 cybercriminals…”, 22 August 2025 (Security Affairs)
- CyberScoop, “Interpol-led crackdown disrupts… $485 million in losses”, 22 August 2025 (CyberScoop)