Encrypted messaging platform Signal has confirmed that a series of targeted phishing attacks have resulted in the takeover of several user accounts, including those belonging to journalists and government officials.
In an official statement shared on its social media channel, the company clarified that the incident did not involve a breach of Signal’s encryption or infrastructure, but instead relied on sophisticated social engineering techniques designed to trick users into revealing authentication information.
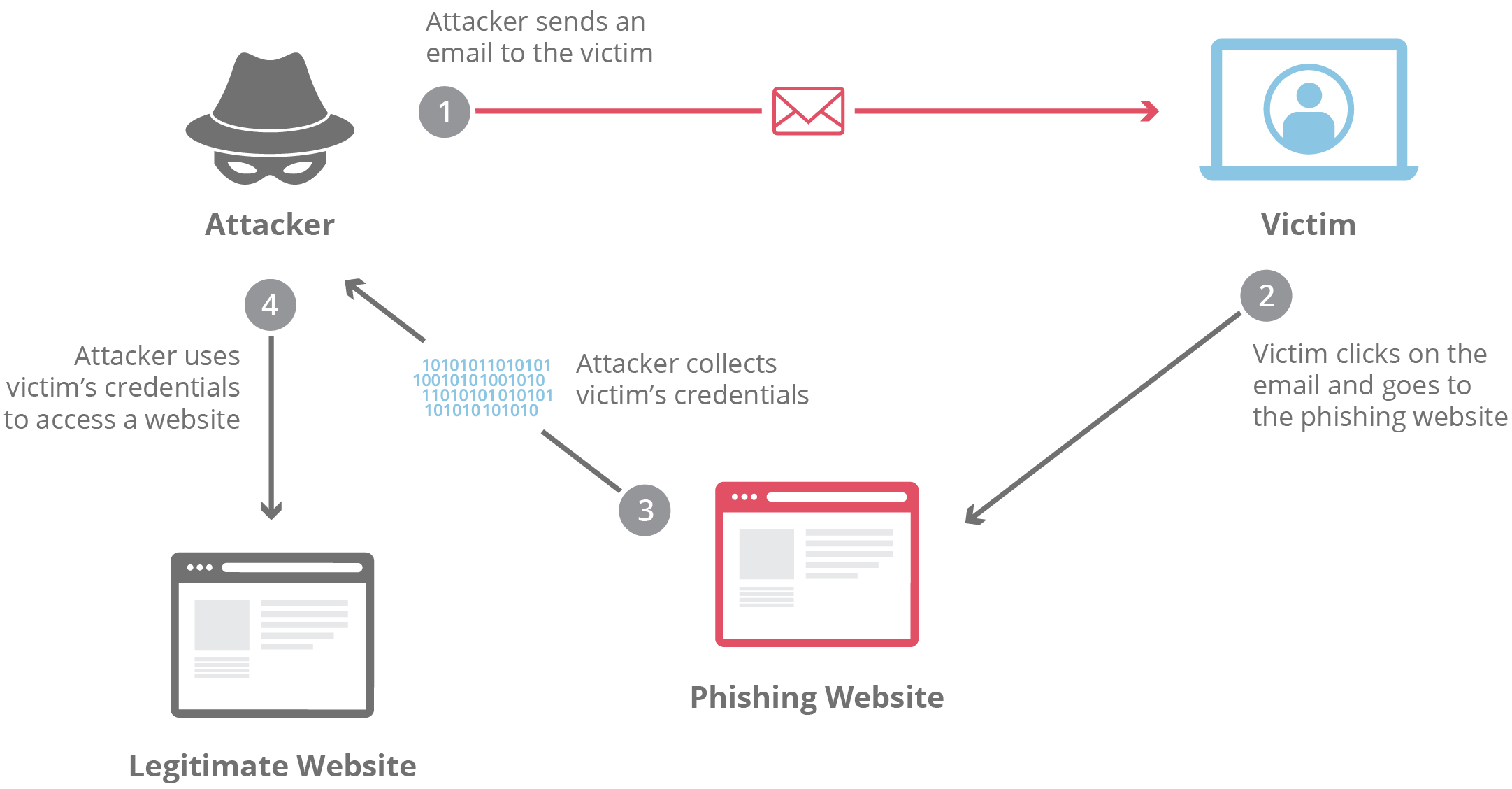
According to Signal, the attackers leveraged phishing campaigns that persuaded victims to disclose SMS verification codes or their Signal PIN, allowing the threat actors to register the victims’ accounts on new devices and gain access.
The company emphasized that the security of its messaging protocol remains intact and that the attacks were conducted through user manipulation rather than a vulnerability in Signal’s systems.
A Social Engineering Attack, Not a Platform Breach
Signal’s announcement comes amid growing concerns about the weaponization of phishing campaigns targeting secure communications platforms.
The attackers’ strategy was straightforward but effective: impersonate trusted contacts or services, then convince victims to share authentication codes or PIN information. Once obtained, the attacker could link the victim’s Signal account to another device, effectively taking control of the account.
Signal clarified in its statement:
“Signal’s encryption and infrastructure have not been compromised and remain robust. These attacks were executed via sophisticated phishing campaigns designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.”
Security experts note that while end-to-end encryption protects messages in transit, it cannot prevent attackers from exploiting the human layer of security.
Why This Matters for Secure Messaging
Signal has long been considered one of the most secure messaging platforms available, widely used by journalists, activists, government officials, and privacy-conscious individuals.
However, the incident highlights a critical cybersecurity reality:
Even the most secure platforms can be compromised if users are tricked into giving away authentication credentials.
This type of attack is particularly dangerous when it targets high-profile individuals because it can expose:
- Sensitive communications
- Sources of journalists
- Government discussions
- Personal or professional contacts
In geopolitically sensitive environments, such access could also be exploited for surveillance, intelligence gathering, or disinformation campaigns.
Growing Trend: Phishing Targeting Secure Apps
Cybersecurity analysts have increasingly observed phishing campaigns targeting secure collaboration tools rather than attempting to break encryption itself.
Instead of attacking the cryptography, attackers focus on:
- Account takeover via authentication codes
- SIM-swap attacks
- Fake login portals
- Social engineering through trusted contacts
This trend reflects a broader shift in cybercrime where identity compromise becomes the easiest entry point into secure digital ecosystems.
For organizations managing sensitive communications, the incident reinforces the importance of user awareness training and strong authentication policies, areas where cybersecurity providers such as Saintynet Cybersecurity often emphasize proactive protection and awareness programs.
Global Security Implications
Because Signal is widely used across media organizations, governments, NGOs, and security professionals worldwide, targeted phishing attacks against its users raise broader concerns.
High-value targets often rely on secure messaging apps for confidential communication. When attackers successfully compromise accounts, they may gain access not only to conversations but also to metadata, trust networks, and operational contacts.
This risk extends across regions including Europe, North America, Asia, and parts of Africa where journalists and activists frequently depend on encrypted messaging tools to protect their sources.
The event also underscores a broader cybersecurity lesson: identity security is now the weakest link in many digital communication systems.
10 Recommended Security Actions
Security teams and individual users should take the following precautions to reduce the risk of account takeover attacks:
- Never share SMS verification codes with anyone, regardless of the request’s urgency.
- Enable Signal’s Registration Lock feature, which protects accounts with a PIN.
- Verify unusual requests from contacts through a secondary communication channel.
- Avoid clicking links sent via unknown or suspicious messages.
- Educate users about phishing tactics and social engineering strategies.
- Implement regular cybersecurity awareness training through programs such as those offered at saintynet.com.
- Monitor for unusual login notifications or device registrations.
- Use strong and unique PINs or passcodes for messaging apps.
- Update mobile devices and applications regularly to ensure the latest security protections.
- Report suspicious messages immediately to security teams or the platform provider.
Organizations looking to strengthen defenses against phishing campaigns should also invest in continuous cybersecurity training and threat awareness initiatives.
Conclusion
Signal’s confirmation of targeted phishing attacks serves as a reminder that secure technology alone cannot eliminate cybersecurity risks.
While Signal’s encryption and infrastructure remain uncompromised, attackers successfully exploited human behavior to gain access to accounts belonging to high-profile users.
As phishing campaigns grow more sophisticated, organizations and individuals must strengthen their identity protection, user awareness, and authentication practices.
In today’s threat landscape, protecting communications is no longer just about encryption, it is about securing the people who use the technology.
CyberCory will continue monitoring developments surrounding targeted attacks on secure communication platforms and provide updates as new information emerges.




